Online security is an incredibly complex topic, yet the vast majority of websites are hacked because they are missing basic security measures that anyone can take. I wrote this with WordPress in mind, but the principles apply to any kind of website.
WARNING Seasoned IT professionals may laugh at the basic points this article touches on. This is not for you, but for mere mortals targeted by script kiddies.

I’ve been in the web hosting business for the last 19 years and almost all of the security incidents I’ve seen did not check one or more of the following five boxes.
Your service provider does have a major role in your hosting account security and it’s natural for humans to look in that direction when things go south. Based on my experience, with hundreds of physical servers we manage and tens of thousands of hosted websites, the vulnerability rarely is at the web hosting provider. In 19 years we’ve never had a physical or virtual server that we manage compromised at “root” level (administrator account on Linux that has access to everything on the server, including all hosted accounts), and just once a system software vulnerability provided access from one hosting account to another on the same server (Apache allowing access to another user’s account via symlinks). That’s not to say that a server cannot be compromised on the system software level. That’s another reason you have step 5 below (backup).
Keep WordPress up to date
When your website is unmaintained, there is no “if” your website is going to be hacked. It’s only “when”. Bits do get rotten. Software vulnerabilities are discovered all the time and it does not take a smart person to hack your site. It does take a smart software developer to discover the vulnerability and to create a script that shows how to exploit it. Usually, responsible developers will not publicly disclose details about the vulnerability, but privately inform WordPress. Once WordPress releases a fix, users will be able to update their installations and WordPress will delay the disclosure some more. But sometimes vulnerability details go public earlier and if you never update your website (or not frequently enough) that delay is not going to help you anyway.
All it takes is a mediocre computer user to run the script on a vulnerable WordPress installation and it’s hacked. We called them script kiddies. You do not have to be a target and you’re not safe because you think you are not a target. Script kiddies automatically scan the web for random WordPress installations, checking which one has a vulnerable version.
If you’re a business owner, do not stop your website investment once the site is built and online. Have a knowledgeable WordPress developer periodically update software and do a security checkup. Ask him to report in a couple of sentences what he’s done.
Use trustworthy and up-to-date plugins
Just as you need to frequently update your WordPress core, you need to update your plugins and your theme.
Not surprisingly, websites are most of the time hacked through plugins, not by exploiting vulnerabilities in WordPress core. After all these years, I’d say that WordPress security is pretty solid. Hard to get the same level of security when adding random plugins.
Keep your plugin count to a minimum. Be very picky when adding yet another plugin to your website. I cannot emphasize this enough. More plugins not only make your website slower, they also offer a wider attack surface.
This is not bullet-proof, but here’s my rule of thumb when selecting a WordPress plugin:
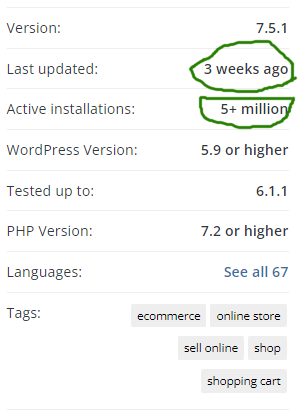
- Does the plugin have a considerable user base? This also depends on how many people would need the features the plugin offers. I expect at least some thousands of installations, even for a rare use case.
- Is the plugin frequently updated and was it recently updated? I’d expect at least an update in the last 1-2 months.
- At least a 4 stars rating, preferably over 4.5. If it’s under 4 stars, I’d start asking questions and dig some more. Users may be unhappy with some missing features, not related to security. Good practice, anyway, to investigate the plugin you’re going into business with.
- Does the plugin support the latest WordPress version? At least the pre-latest, as the latest may have just been published. Just another check to confirm that the plugin is actively developed.
If you’re not using a plugin or a theme, uninstall it. It’s just an unnecessary potential attack vector.
Use strong passwords and two-factor authentication
You know this by now. But what is a strong password and how do you remember a complex password?
The password is more secure the longer it is and the greater the character variety. But you won’t remember a password like “xe*(#DKHD3kh3”. Here come those password storage and management applications. Watch out for their own security incidents.
Here are three options for you:
- Remembering the password. Between a longer password, but with some meaningful words (which makes it easier to remember) and a shorter password but with highly random characters, choose the former. “Eva$sales 2Crabfish” is secure and pretty easy to remember after a few repetitions. Note how individual words have meaning (which makes the password easier to remember), but the word combination is incorrect and you have lowercase, uppercase characters, a space, a number, and a dollar sign. “i9802#W$jh” is, surprisingly or not, less secure and harder to remember. The idea is not to use anything that can be predicted by another human being. Be creative and go a bit random. A novel title, even if it’s long, is not a good password.
- If you’ll use a password management application, choose one that only stores your data locally. Storage in the cloud, even if it’s encrypted with your master password and theoretically only you can decrypt it, still raises some questions.
- Use Single Sign-On from a reputable provider like Google or Microsoft. This way you can have a single strong password that you remember, you use it for many websites (still, the encrypted password is only stored at one authentication provider) and you benefit from the advanced protection mechanisms of a trustworthy provider. You can even go wild with an Advanced Protection Program.
Regardless of how you are managing the password authentication, always use two-factor authentication.
Your password may leak through an unfortunate event. Maybe a phishing email, a virus, a stolen laptop, or anything else. Search for and install a WordPress plugin that offers two-factor authentication.
Are you using your email account password when you sign up to order something from a random website? Bad idea. That random website may be set up to show your password in plain text to an administrator. He could be reading your email right now. Not nice, against best practices, but it can happen and you cannot control it. Do not use the same password on different websites. Always use unique passwords or single sign-on.
Secure your workstation
Wait a minute, what does my laptop or my PC have with my website security? Well, if I had a nickel for every virus that infected a PC that had the email/FTP/cPanel password saved on it… That’s right. This is a common attack vector. Ensure you have up-to-date antivirus and watch your link-clicking and anti-phishing hygiene.
I have seen the following story a few times. The loss may be in the tens of thousands of euro range and rarely recovered.
The attacker finds out your email account or cPanel password. He may find it through a virus on your PC, by tricking you with a phishing email, or by guesswork. Then he logs in to your account and configures your email to Cc all messages to some other email account he owns. He notices that you’re talking to a company from Italy about buying an excavator (this is a true story). When the negotiations are over and you’re ready to pay, you get the invoice, and you make the payment. Just that you paid the attacker, not the real seller. The attacker, knowing everything that was discussed, emails you an apparently legitimate invoice from an apparently legitimate email address (thecompany.accounting@gmail/outlook). Watch out for those email From fields, the links, and the bank account owner’s name. It may cost you dearly!
You’re only human and you’ve just got scammed for 50,000€. So, you call the kind folks from the web hosting company and tell them that they have a security problem! We dig through the logs and manage to point out the whole chain of events: successful cPanel authentication from an unexpected IP and country and emails CC-ed to some suspect free email account. We reported everything to the police and our customer was optimistic because the bandits were caught (not their first hit) and they were about to recover the money. Hope they did, I think it is rarely the case.
If someone knows your email, FTP, or cPanel password, your website is obviously at risk, as well.
Checklist to avoid this kind of scam:
- Strong, unique passwords and two-factor authentication everywhere
- Workstation security
- Educate yourself and your people on email phishing.
Extra step: encrypt your workstation storage. This feature is usually provided by the operating system, and you should enable it. Why? If you lose your laptop or it gets stolen, someone may open it, take out the SSD, connect it to another system, and read all your data. They do not need your local user password for this.
Back up and test the backup
There are two kinds of people in the world: those who back up and those who will back up.
If you’re in business long enough, you will get to a point when you desperately need that backup. “Hoping is not a strategy” applies here very well.
Let’s see when you need a backup:
- You edit or delete content by mistake. Luckily, you have WordPress post revisions. But if things can go wrong, they will go wrong, like deleting images via FTP.
- A software change or update that went wrong may completely break your website. Use a staging copy of the live website to test changes before changing the production website.
- Compromised website. As diligent as you may be, sometimes you just have bad luck. You may even live with the enemy in your own house. Your website may have been compromised months ago and you don’t even know it. This is when you need older backup copies, not just from a month ago. Once the site is compromised, one ugly scheme is that they redirect some of your customers’ payments to their payment gateway instead of yours. Just some, this way you won’t notice immediately.
There are two kinds of backup: your web hosting company’s backup and your own backup, completely independent from your WordPress hosting provider. Make sure you have both.
First, make sure you have the backup and recovery operations included with your hosting subscription. Some companies charge extra for backup, and it may not be included with your subscription. Ask yourself and the provider some questions. Do they back up? How frequently? How long do they store it? How long does it take to recover data from the backup? Do they charge extra for backup recovery? Test it. Ask your hosting provider if they can give you an archive with your database and your website files from a month ago.
Even the best provider may mess up sometimes. Do not hope that your 5€ monthly subscription will cover your 10,000€ loss in website development costs or sales. The web hosting subscription is not business insurance. Put in place an additional, independent backup process. Prepare your disaster recovery plan that empowers you to be online in a short time span even if your provider has a long downtime.
Test the backup. Periodically test disaster recovery scenarios. That automatic monthly backup process may be a silently failing automatic process. I’ve seen it happen.
Is that all?
No publicly available website is 100% secure, otherwise, huge companies, with deep pockets, would not leak millions of customer credit cards. But with these security measures you are 94% covered (the number comes from an elaborate statistic based on holding my wet finger in the wind, still, you’ll be way better than many websites).
These are simple steps that you can implement yourself without deep technical knowledge. To take this further, you need to talk to a company that specializes in IT security. More elaborate attacks may specifically target your company and usually involve social engineering. You should be in the deep-pockets league by then.

Carlo
Hi,
I’ve notice you have a special offering for WordPress hosting. How is this different from a reguluar cPanel account?
Adrian Andreias
Hey Carlo!
Our WordPress Pro hosting packages offer a more powerful solution than a common shared hosting account. WordPreas Pro includes more memory, more CPU power, more powerful hardware (NVMe storage and newer CPU models), a dedicated private service for Redis caching and many more features. These will make your WordPress website faster, even if it’s a high resource consumer.
There are also standard features that make our service loved by our customers: 24/7 fast email and phone support, LiteSpeed – fast web server software, BitNinja protection, free migration etc.
Let me know if you have any other questions.